Latest Story
-
White reef grief
Open Forum | April 18, 2024The summer of 2023−24 saw substantial climate driven impacts across the Great Barrier Reef, with widespread coral bleaching, two cyclones and several severe flood events.
-
Bouncing back from the dead
Open Forum | April 18, 2024Palaeontologists from Flinders University have identified three species of giant kangaroos from Australia and New Guinea which lived from around 5 million to 40,000 years ago before they were wiped out by man.
-
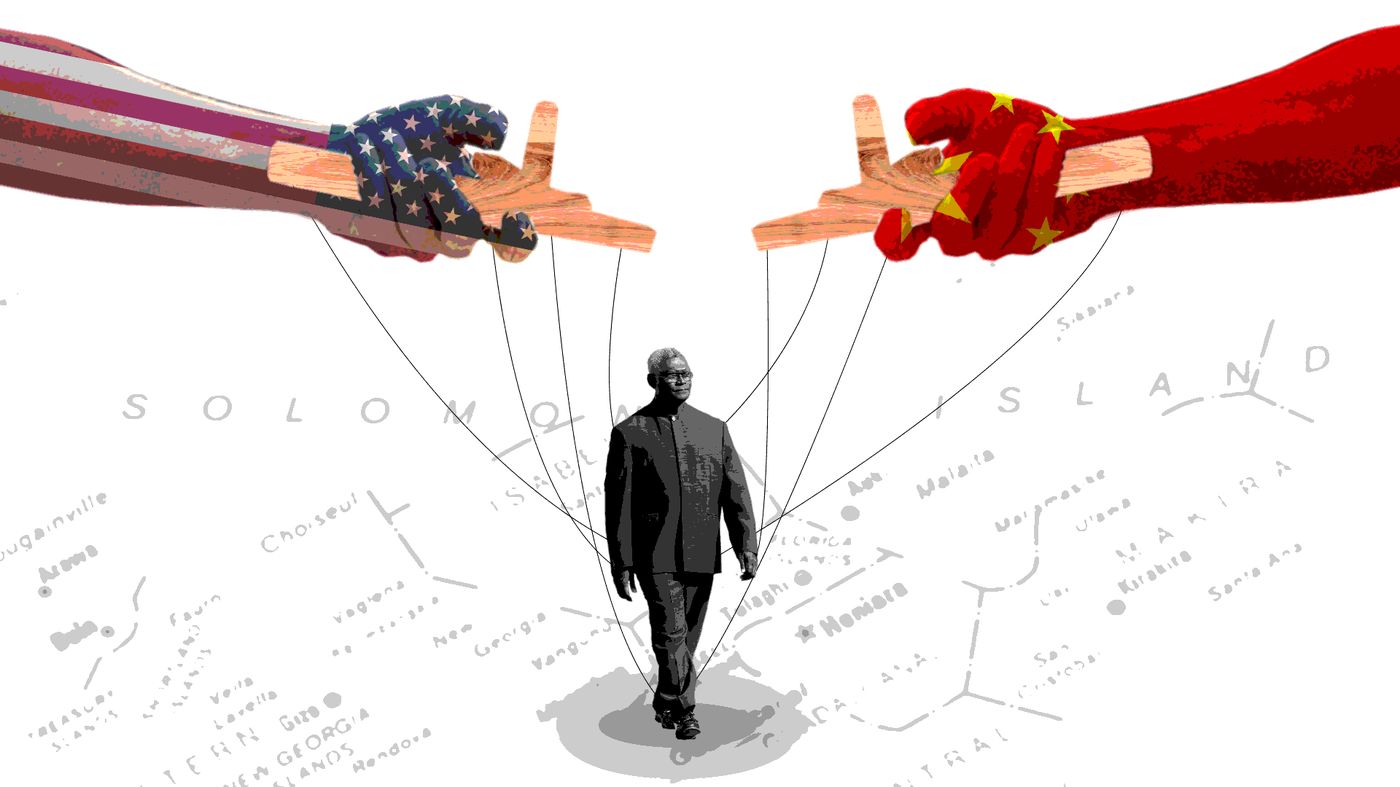
Buying friends and influencing people
Teuku Riefky | April 18, 2024The Solomon Islands election will be watched closely by both Beijing and Washington, and test the success of China’s policy of buying political influence in the region.
-
Women still see politics as a male-dominated domain
Open Forum | April 17, 2024Despite growing momentum to increase female representation in Australia’s national parliament, it continues to be a male dominated domain. New research from Monash University explores why young women still feel reluctant to become a member of the national parliament.
-
Encouraging critical thinking in schools
Geoffrey Dobson | April 17, 2024Better education, combined with social media regulation, can help to combat the plague of science denial on popular platforms like tik-tok.
-
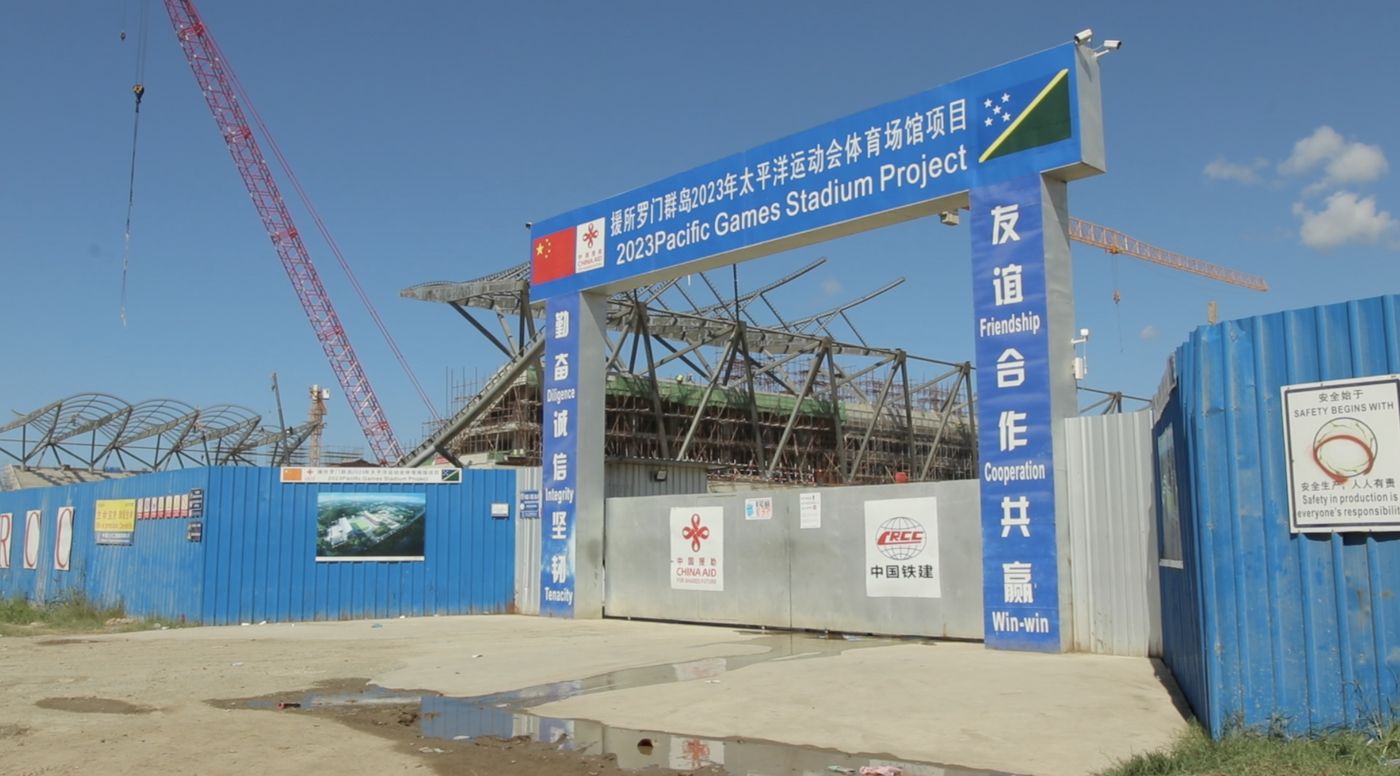
Will China win the Solomon Islands election?
Priestley Habru | April 17, 2024The overbearing economic, political and security influence of China will weigh heavily on the Solomon Islands election.
-
Trust the science
Doug Hilton | April 16, 2024We need science to tackle the big challenges of today, so we must defend it from attack. While Australia isn’t as polarised as the US about scientific trust and issues, we can’t afford to be complacent.
-
Understanding the Solomons elections
Priestley Habru | April 16, 2024Prime Minister Manasseh Sogavare is looking to retain power on April 17 in what could prove a vital day for the geo-political future not just of the Solomon Islands, but the whole Pacific.
-
Innovate and grow
Open Forum | April 16, 2024Australia’s national science agency, CSIRO, is inviting small to medium enterprises (SMEs) working on advanced manufacturing solutions to apply for a self-paced, 10-week, online program that can help them turn an idea into an R&D opportunity.
-
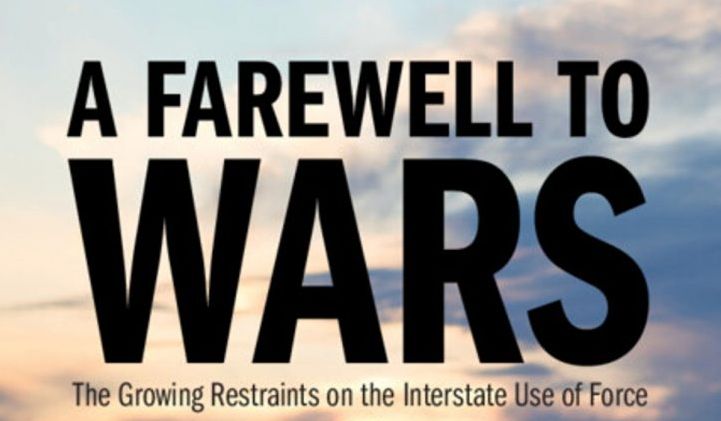
A farewell to arms?
John Tilemann | April 15, 2024With war raging in Ukraine and the Middle East it’s difficult to remember that the international system has accepted growing constraints on interstate use of force in most circumstances.
-
Mapping global cybercrime
Open Forum | April 15, 2024Three years of intensive research by an international team of researchers has informed the first ‘World Cybercrime Index’ which ranks Russia as the major threat to global cyber security.
-
Science is the key to our manufacturing future
Open Forum | April 15, 2024The Australian Academy of Science has welcomed the Prime Minister’s intention to legislate a “Future Made in Australia Act” to boost technologically advanced manufacturing in this country.